GoPlus has discovered a high-risk vulnerability in Claude Chrome that can silently allow theft of Gmail and Drive data.
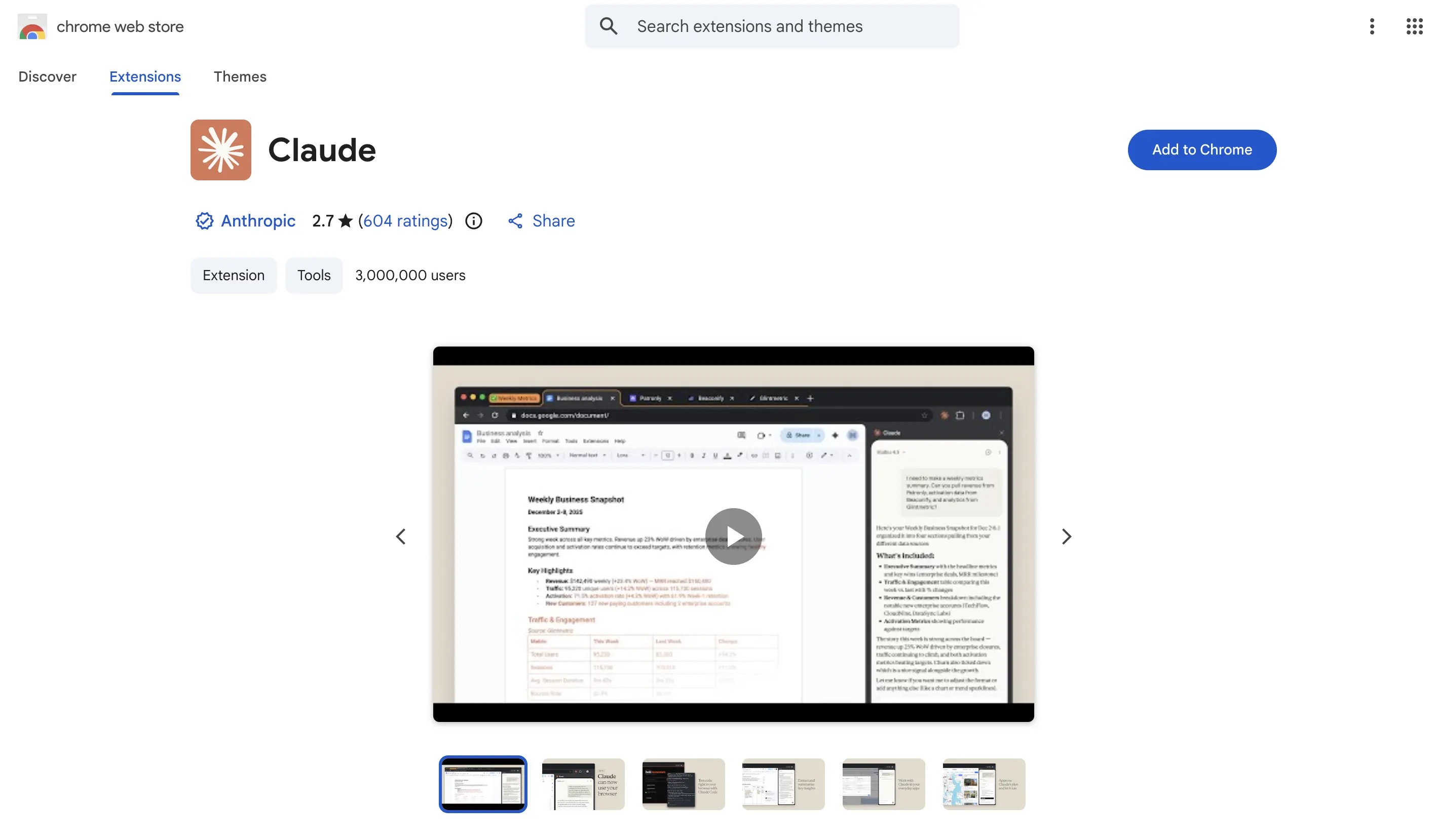
The security monitoring platform GoPlus issued a high-risk alert on March 27, indicating that the Anthropic Claude Chrome browser extension has a critical prompt injection vulnerability affecting installations below version 1.0.41, impacting over 3 million users. Attackers can read Google Drive documents, steal business tokens, and send emails as the user.
Vulnerability Principle: Two Weaknesses Combine to Form a Complete Attack Chain
This vulnerability consists of a combination of two independent security flaws that create a high-risk attack path.
First Weakness: The overly broad subdomain trust of the Claude Chrome extension’s messaging mechanism allows commands from all *.claude.ai subdomains to pass through, one message type, onboarding_task, directly accepts external prompts to be executed by Claude without finer source validation.
Second Weakness: The DOM-based XSS vulnerability in the Arkose Labs CAPTCHA component. Anthropic uses the third-party CAPTCHA provider Arkose Labs, whose CAPTCHA component is hosted on a-cdn.claude.ai—a subdomain that falls within the *.claude.ai trust scope. Security researchers discovered a DOM-based XSS vulnerability in an older version of the CAPTCHA component: the component never verified the sender’s identity (did not check event.origin) when receiving external messages and rendered user-controllable strings directly as HTML without any sanitization.
Complete Attack Chain: Victim visits a malicious webpage → Background silently loads the Arkose iframe with the XSS vulnerability → Injects malicious payload executed within the a-cdn.claude.ai domain → Exploits the subdomain trust whitelist to send malicious prompts to the Claude extension and executes them automatically. The entire process occurs in an invisible hidden iframe, completely undetectable by the victim.
What Can Attackers Do: Account Taken Over Without Awareness
Once the attack is successful, attackers can perform the following actions on the victim’s account without any user authorization or clicks:
· Steal Gmail access tokens (persistent access to Gmail and contacts)
· Read all documents in Google Drive
· Export complete chat history from Claude
· Send emails as the victim
· Open new tabs in the background, open the Claude sidebar, and execute arbitrary commands
Fix Status and Security Recommendations
The vulnerability has been fully patched: Anthropic patched the Claude Chrome extension on January 15, 2026, allowing requests only from specific sources; Arkose Labs fixed the XSS vulnerability on February 19, 2026, with thorough retesting on February 24, 2026, confirming the issue was resolved. GoPlus’s alert aims to remind users still using older versions to upgrade promptly.
GoPlus offers the following security recommendations: Go to the Chrome browser at chrome://extensions, find the Claude extension, and ensure the version number is 1.0.41 or higher; be cautious of phishing links from unknown sources; AI Agent applications should follow the “least privilege principle”; and introduce a human-in-the-loop mechanism for operations involving high sensitivity.
Frequently Asked Questions
How can I confirm if my Claude Chrome extension version is safe?
Go to the Chrome browser at chrome://extensions, find the Claude extension, and check the version number. If the version is 1.0.41 or higher, the vulnerability has been patched; if it is below 1.0.41, please update or reinstall the latest version immediately.
Does this vulnerability require the user to actively click a malicious link to be triggered?
No, it does not. As long as the user visits the malicious webpage, the attack can execute silently in the background without any clicks, authorizations, or confirmations. The entire attack chain is completed in a hidden iframe, completely undetectable by the victim.
Anthropic has completed the fix, so why is an update still necessary?
Some users may not have enabled automatic updates for the browser extension, resulting in them still using an outdated version below 1.0.41. GoPlus’s alert aims to remind these users to actively check their version and manually upgrade to ensure safety.