How does Jasmy operate? A detailed breakdown of the complete workflow from personal data creation to data transactions
Interest in Jasmy’s operational workflow stems from the fact that it’s not just another token project—it’s a comprehensive system built around personal data, IoT devices, enterprise data needs, and data transactions. Understanding this workflow is crucial for assessing how Jasmy converts “personal data control” into a functional, scalable data economy.
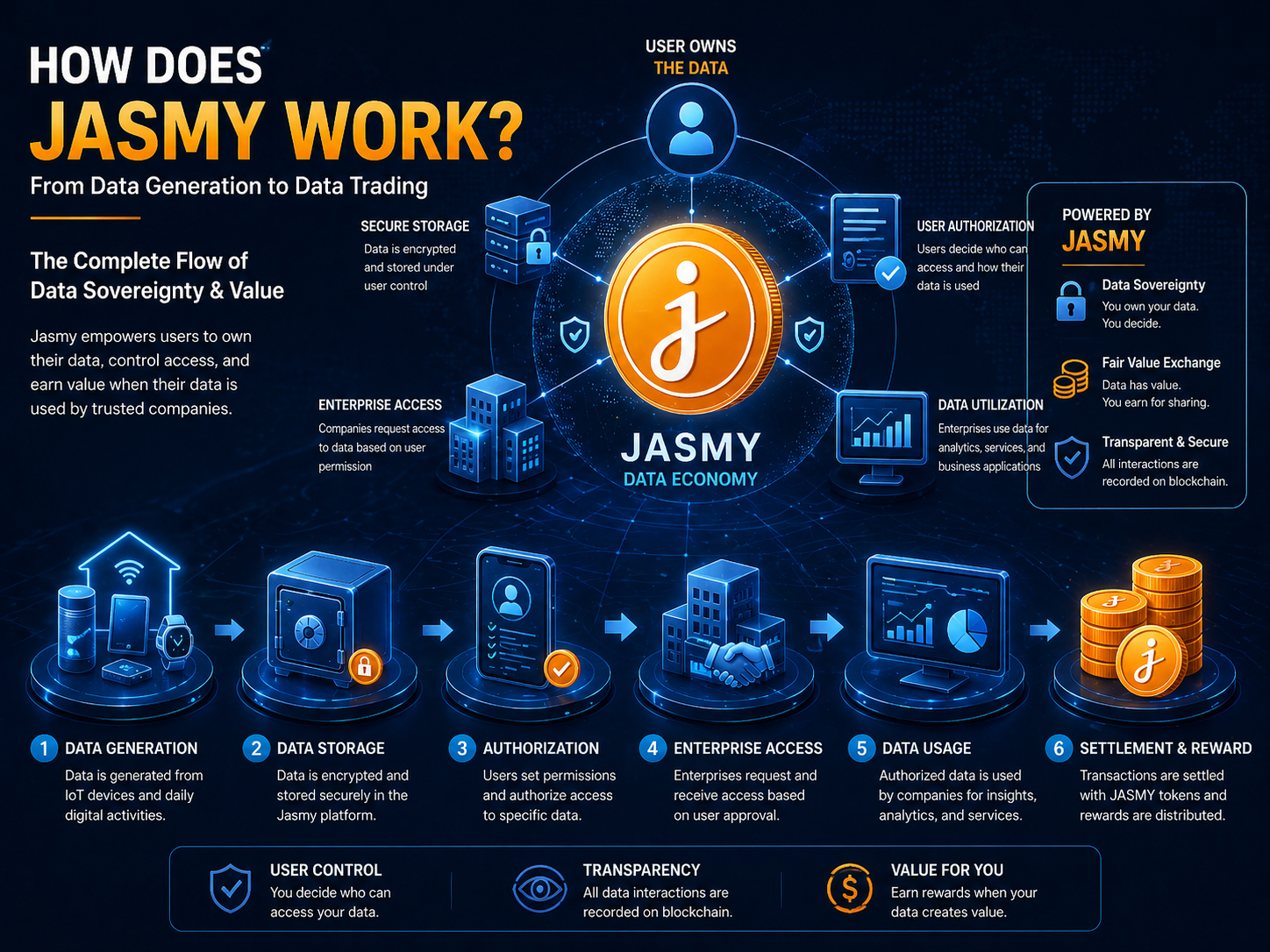
The process typically includes data generation, data storage, access authorization, enterprise utilization, transaction settlement, and revenue allocation.
Jasmy Data Flow Overview: How Personal Data Becomes Valuable
Jasmy’s data flow centers on “user-controlled data,” with the primary goal of transforming personal data from passive collection into a digital asset that users can authorize, track, and settle.
From a process perspective, users generate data via devices or apps, and this data is then stored in a user-controlled environment. Users determine, based on context, whether to grant enterprises access. Once authorized, enterprises can leverage the data for analytics, service optimization, or commercial applications, and settle payments using JASMY tokens.
| Stage | User Action | System Functionality | Purpose |
|---|---|---|---|
| Data Generation | Using devices/services | Creating personal data records | Establishing data sources |
| Data Storage | Managing personal data | Controlled storage | Retaining user control |
| Data Authorization | Defining access scope | Setting permissions | Controlling data utilization |
| Enterprise Utilization | Enterprise requests data | Access per authorization | Enabling business applications |
| Transaction Settlement | Value exchange | Settlement via JASMY | Powering the data economy |
This workflow empowers users, turning data from a platform-owned resource into an asset they control and share in its value. Jasmy integrates data sovereignty, blockchain records, and tokenized settlements to facilitate this shift.
How User Data Is Generated and Stored (IoT & Personal Data)
User data within Jasmy originates from everyday digital activity and IoT device interactions, making the value proposition dependent on authentic behavior, usage patterns, and device status.
Smartphones, smart home devices, vehicles, wearables, and other connected hardware all generate data—such as location, device status, usage frequency, behavioral preferences, or health metrics. Traditionally, internet platforms collect this data centrally; Jasmy, by contrast, shifts management and control to the user.
After data is generated, it’s stored in an environment users manage, not simply handed over to a platform. Data storage isn’t just about retention—it includes confirming ownership, controlling access pathways, and recording usage history.
This stage is crucial: it determines whether the data economy can truly be built on user empowerment. Without user-managed data, subsequent authorization, trading, and profit-sharing would be impossible.
How Data Is Authorized in Jasmy (Access Control Mechanisms)
Jasmy’s authorization process determines who can access data, which data is accessible, and under what conditions it can be used.
Authorization doesn’t mean surrendering data outright. Users specify access scopes based on their needs, and enterprises must comply with these permissions. The system logs the authorization process, ensuring all access is auditable.
The mechanism operates on three levels: users identify data types (device data, behavioral data, identity information), the system generates access rules to restrict enterprise reach, and enterprises use data within the authorized scope, settling value through the platform.
The key is that users retain control. Enterprises cannot access data without permission, and users decide if and how their data is shared.
This framework makes Jasmy’s data sovereignty vision operational and ensures data transactions have clear boundaries.
How Enterprises Access and Use Data (Data Access & Business Scenarios)
In the Jasmy ecosystem, enterprises acquire data only after obtaining user authorization and adhering to access rules.
The workflow: enterprises articulate their data needs—such as user profiling, device behavior, market analysis, or service optimization. The system matches available data per user authorization. Enterprises receive access, limited to the user-approved scope.
This approach offers enterprises transparent, compliant data sources. Compared to traditional collection, authorized data builds trust and fits business scenarios where user confidence is required.
Enterprises deploy data for product improvement, user research, IoT device management, identity verification, or personalized services. Upon completion, the platform records usage and settles the transaction.
The critical balance: enterprises get actionable data, users retain control, and the platform facilitates and enforces the rules.
How Data Transactions and Settlement Work (JASMY Payment Workflow)
Jasmy executes data transactions via authorized access and settlement with JASMY tokens—converting data usage into measurable, economic activity.
In these transactions, enterprises aren’t buying users—they’re purchasing access rights to specific data sets. After users grant authorization, enterprises pay JASMY to access data, and the platform logs and settles the transaction.
Data trading follows a clear sequence: enterprises request data, users confirm authorization scope, enterprises pay in tokens, and the system records access and distributes revenue.
This mechanism clarifies data value: unlike traditional models where platforms collect user data for free and monetize it, Jasmy ties data access to payment, rewarding users for participation.
JASMY serves as the settlement medium, standardizing value exchange in data transactions.
How Revenue Is Shared Between Users and the Platform (Data Economy Model)
Jasmy’s revenue model centers on users, enterprises, and the platform—ensuring data contributors participate in value flows.
Users provide and authorize data, enterprises pay JASMY for usage rights, and the platform records access, enforces rules, and manages settlement. Revenue distribution relies on confirmed and recorded data access.
User earnings come from authorizations, enterprise value from data utilization, and platform value from matchmaking, rule enforcement, and infrastructure services. This forms a data-driven economic cycle.
This model disrupts the traditional “platform-centric profit” structure: users become stakeholders, not just data sources.
Sustainable operation depends on data quality, enterprise demand, user engagement, and platform efficiency. Only continuous participation ensures a stable data economy.
Summary
Jasmy’s workflow covers personal data generation, storage, authorization, enterprise utilization, transaction settlement, and revenue sharing. The core is empowering users with data sovereignty and enabling value exchange via JASMY. This links IoT data, blockchain records, and a tokenized data economy, giving personal data attributes of management, authorization, and settlement.
FAQ
How does Jasmy work?
Jasmy establishes a data flow through personal data storage, authorized access, and tokenized settlement. Users control access permissions, enterprises use data within those permissions, and settlement occurs via JASMY.
How does user data enter the Jasmy system?
User data is sourced from IoT devices, application services, and everyday digital activity. Once stored in a controlled environment, users decide on enterprise access authorization.
How does Jasmy implement data authorization?
Jasmy uses access control to restrict enterprise data usage. Users determine whether to share data, with whom, and for what purpose.
How do enterprises use Jasmy data?
Enterprises must obtain user authorization to access data, which is then used for analytics, service optimization, device management, or commercial purposes. Access is logged and used for settlement.
What is JASMY’s role in data transactions?
JASMY is the payment and settlement token for data access. Enterprises pay JASMY to obtain authorized data, and users earn rewards for sharing their data.
Related Articles

The Future of Cross-Chain Bridges: Full-Chain Interoperability Becomes Inevitable, Liquidity Bridges Will Decline

Solana Need L2s And Appchains?

Sui: How are users leveraging its speed, security, & scalability?

Navigating the Zero Knowledge Landscape

What is Tronscan and How Can You Use it in 2025?


